Forecast Risks to Better Avoid Them
Model and Simulate Changes to Risk for any Action

Model and simulate risk

Unleash the Power of Certainty
With Asimily, foresight becomes your greatest ally. Envision, predict, and act with unparalleled confidence, and unlock a new era of proactive risk mitigation.
Get in TouchModel and Simulate Risks Before Any Action
Avoid Risk From the Start
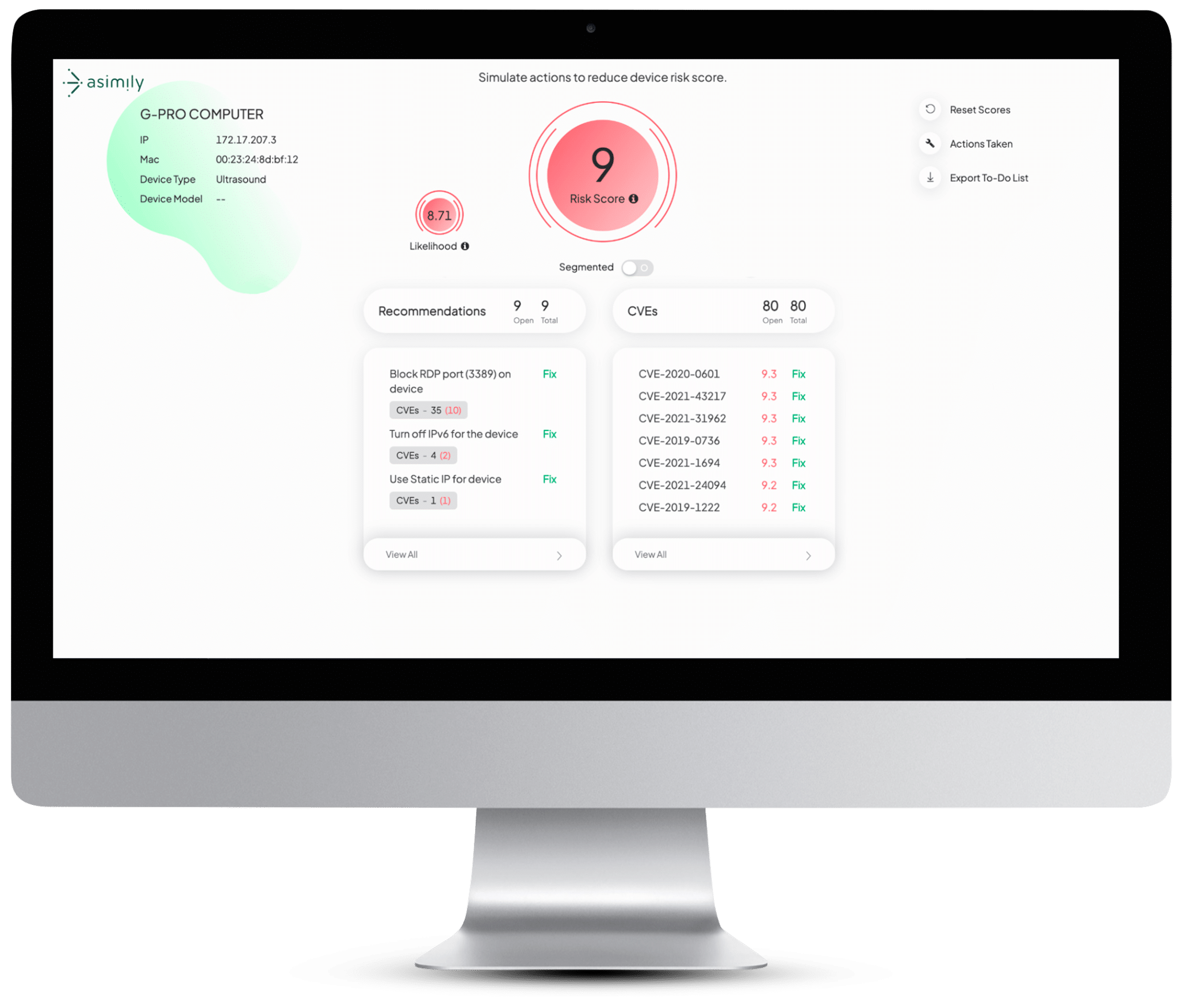
Simulate Device Risk Scenarios
Calculate the least risk associated with a device before configuration and connection.
Avoid Buying Risky Devices
Avoid installing risky device configurations by knowing the safest one. Asimily manages and shares the most secure, active configurations of devices across our customer set, so you can be as safe as the safest.
Get Time Back for Your Team
With Risk Simulation, potential changes to devices and networks to mitigate vulnerabilities can be tried out, virtually. See how Risk Scores change without lifting a finger; pick the best risk reduction for your team’s available time.
Benchmark Your Risk
Risk Scores are calculated automatically for your organization, your peers, and for each device. See progress over time, and how you rank relative to similar institutions.
Model Risks to Demonstrate Better Compliance
Pre-Purchase Risk Modeling
With an extensive database of devices, see the risk that comes with any purchase of a networked device. Work with teams to get the safest device that meets organizational needs with data in hand.
Simulate Risks to Plan Work Better
With a simple click of a button, see the risk reduction that comes from any of Asimily’s hundreds of targeted remediation guidance steps. Pick your tasks based on the time cost and risk reduction to work efficiently.
Avoid Hidden Security Costs
Some devices come with hidden secrets and poor security. Less safe versions of devices can require upgrades, configurations and segmentation to reduce risk. Know before you buy to plan better.
Avoid Unsafe Configurations
See the safest known operating configuration for your devices, based on functioning installations across the Asimily customer base, avoiding trial and error that others have done before you.
Secure Every IoT Device.
Automatically.
Cyber threats move fast — so should you. Asimily gives instant inventory and smart, prioritized risk mitigation insights for every IoT, OT, and IoMT device — so you can take action before threats strike.
Protecting Your Industry’s Unique Devices
Healthcare
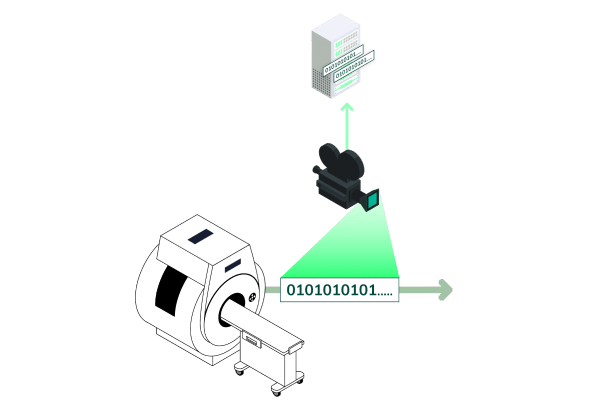
Asimily provides the necessary tools to identify and address IoT vulnerabilities in healthcare, ensuring the protection of patient data without interrupting the delivery of critical care.
Discover MoreManufacturing
In an industry that relies heavily on IoT devices to drive automation, efficiency, and connectivity, Asimly can help. By ensuring the security of IoT devices, manufacturers can safeguard their intellectual property, prevent production disruptions, and maintain the trust of their customers and partners.
Discover MoreHigher Education
Educational institutions depend on interconnected devices to facilitate learning, research, and campus operations. Protect sensitive student and faculty data, maintain operational integrity, and foster a secure, productive academic environment with Asimily.
Discover MoreGovernment
Asimily equips government entities worldwide with the necessary tools to secure their IoT devices, protect critical infrastructure, and ensure data privacy. Defend against cyber threats and uphold public trust by proactively mitigating vulnerabilities.
Discover MoreLife Sciences
Where delicate research, development, and data exchange are ongoing, securing your IoT devices is a top priority. Proactively manage and mitigate vulnerabilities, reducing the risk of theft or loss of critical research and development efforts.
Discover MoreFrequently asked questions
IoT Risk modeling is a set of capabilities that allow an organization to see the risk associated with networked devices. It also includes changes in risk, associated with specific actions. The risk is calculated without needing to make real-world changes.
It’s like a spreadsheet for risk. Organizations can see what scenarios of devices and remediation lead to what level of risk. It allows many hypothetical situations to be considered, before taking real-world action to achieve one of them.
Risk modeling has three major components – device risk scores, remediation risk simulation, and overall organizational risk.
By adopting a proactive risk management approach, you can address vulnerabilities, make informed risk mitigation decisions, and maintain a strong security posture. This will ultimately result in reduced downtime, enhanced data protection, and improved overall resilience.
Yes, by being able to have a complete picture of devices and the work needed to secure them, a significant hidden cost can be reduced. This lets organizations buy secure devices from the start. Further, high-effort tasks can be compared to low-effort tasks, to pick the most efficient risk reduction possible.
Absolutely! Asimily’s risk modeling is designed to cater to various industries, including healthcare, life sciences, higher education, and more. Our platform’s adaptive capabilities allow it to address the unique cybersecurity challenges of different sectors, ensuring you stay ahead of threats regardless of your industry.