Vulnerability Prioritization for IoMT Security and Risk Management

Today’s healthcare delivery organizations (HDOs) face a unique challenge. As an HDO onboards more Internet of Medical Things (IoMT) devices, its already understaffed Health Technology Management (HTM), IT, and security teams struggle to gain shared, holistic visibility across devices and network security risks. Meanwhile, attacks against HDOs continue to increase in volume and severity with Ponemon’s Cyber Insecurity in Healthcare report noting that 89% of HDOs experienced an average of 43 attacks in the last twelve months.
For improved IoMT security and risk management, HDOs need a solution that provides HTM, IT, and security teams with the visibility and vulnerability prioritization they need to effectively secure medical and IoT devices.
Although all working toward a common goal, the proliferation of IoMT devices creates a gray area, one where no single team has all the skills to manage the vulnerability prioritization and management, network, and security functions alone. HTM teams are device performance experts, who are sometimes tasked with cybersecurity. IT teams usually have cybersecurity expertise but do not deal with the myriad of IoMT devices in the world regularly. With each IoMT device containing an average of 6.2 vulnerabilities, these teams need a shared, aggregated source of device, vulnerability, and security information.
Fortunately, several different IoMT security companies offer viable solutions to these challenges. The tricky part is knowing which one to choose based on your organization’s needs.
What is IoMT?
The Internet of Medical Things (IoMT) is a subset of Internet of Things (IoT) technologies and consists of medical devices and applications that connect to an HDO’s networks and other devices. Some examples of IoMT devices include:
- Heart Monitors
- Infusion IV Pumps
- Radiology equipment including CT Scanners, MRI Machines, CArms, X Rays
- Pulse Oximeters
- Surgical robotics
- Lab microscopes and refrigerators
- Anesthesia machines
- Aspiration/Suction Pumps
- Glucose Monitors
Historically, these devices were standalone instruments, only interacting with a medical provider and patient. Today, these connected medical devices connect to the HDO’s systems and networks, enabling various benefits like:
- Improved treatments and cost savings
- Faster and precise diagnostics, as IoMT technology can track patient’s vital signs in-depth and detail
- Better patient monitoring, without requiring visits to a medical facility
Understanding IoMT Trends and Security Risks
While IoMT can improve the healthcare delivery processes, it creates additional security risks.
IoMT is here for the long term. According to one report, the global IoMT market is expected to reach $187.60 billion by 2028, more than four times its $41.17 billion worth in 2020.
Simultaneously, every new device connected to HDO networks creates a new attack vector via the internet. IT and security practitioners in the healthcare industry recognize these risks, as evidenced by the recent Ponemon Institute report identifying their top three cybersecurity concerns:
- Insecure medical devices (64%)
- Ransomware (60%)
- Insecure mobile apps/eHealth (59%)
Security Risks
Attackers have always and will continue to target the healthcare vertical because it maintains vast amounts of sensitive patient data.
According to the 2022 IBM Data Breach Investigations Report (DBIR), healthcare industry data breaches were:
- $10.1 million per incident in 2022
- 9.4% more costly in 2022 compared to 2021
- 80% higher than the $4.35 million data breach cost global average
These costs make sense as the research also noted that HDOs take almost 11 months to find and neutralize a breach, meaning attackers have more time to steal sensitive data.
For HDOs, security risks go beyond just the costs associated with the data breach response itself. Across complex, IoMT-connected environments, attacks can lead to:
- Delayed procedures and tests that harm patient health outcomes
- Interruption of life-saving services
- Increased mortality rates
- HIPAA Fines and Investigations
- Legal Liability
- Reputation Damage
- Decrease in New Customers
With the average hospital operating margin at 1.4% in 2023, the aggregated financial, reputational, compliance, and legal costs arising from a data breach and service interruption undermining patient health can lead to bankruptcy and closure.
More Than Traditional Vulnerability Scanners Can Manage
As HTM, IT, and security teams try to secure this expanded device landscape, they often lack a single point of device information. The IT team’s traditional vulnerability scanning technologies can cause service outages for IoMT devices, negatively impacting patient health and care. The HTM team lacks visibility into the devices connected to the network and their vulnerabilities. The security team has no way to monitor endpoint and network security holistically.
Automated Configuration Changes
Most IT teams use active network and vulnerability scanners that detect devices and take automated action. In the IT environment, the configuration changes enhance security and reduce manual labor. For example, if the scanner detects a laptop with a known vulnerability, it can block the device from the network.
However, with IoMT, automated actions can undermine patient care. For example, the automated removal of an infusion pump means the device may no longer provide accurate readings and critical medication dosages
Legacy Technologies
From the IT and security team perspective, devices designated End of Life (EoL) are inherently risky since the manufacturer no longer supports operating system or software security updates and patches. However, medical devices often have longer lifespans because they are so expensive, sometimes millions of dollars. These EoL situations create a security risk because attackers often exploit known vulnerabilities to gain unauthorized access to healthcare systems and networks.
For example, an HDO might have an MRI machine built ten years ago that uses either Windows 7 or Windows XP operating system. The expensive device was built to last ten years, but ten years ago no one expected these devices to have so many potential connections to the public internet. HDOs need to implement security controls to mitigate the risks arising from the known vulnerabilities in these EoL devices.
HDOs often leave these technologies in their environments or various reasons:
- Lack of budget for new technologies
- Risk mitigation by maintaining known, reliable systems
- Lack of staff or expertise to upgrade software and systems
Identify Exploitable Vulnerabilities & Prescribe Mitigation Strategies
When vulnerable assets are identified, the next step is to create a mitigation strategy. IoT security companies should help you with both efforts. The most accurate risk analyses come from combining technology with human verification.
Technology provides advanced risk analysis and maps out the relationships between devices and networks. Human verification then fills in any gaps and acts as a tool to ensure accuracy. Your risk remediation platform should offer tailored mitigation strategies when critical vulnerabilities are found.
Security practices vary in the effort it takes to implement them. An easy patch and a complex micro-segmentation are very different, especially when your team is strapped for time. It may be advisable to look into other methods to fence-in devices away from attack methodologies, such as disabling services and restricting user access.
Too often, vulnerability information in the industry stops with only the easily accessible and basic vulnerability disclosure information. Vulnerability Prioritization and Management within Asimily identifies exploitable flaws in your medical device ecosystem quickly. In addition, our platform prescribes the most efficient mitigation strategies for each vulnerable asset and provides detailed instructions on implementing them. Depending on your preference, threat response can be automatic or manual.
5 Ways to Mitigate IoMT Security Risks
To mitigate IoMT security risks, HTM, IT, and security teams need a solution that enables them to respond to these devices’ needs, giving everyone the visibility they need so that they can coordinate activities across the diverse, interconnected environment.
1. Use Passive Scanning Built for IoMT Devices
Passive scanners discover and classify medical devices without changing the device’s configurations or readings while inpatient use. Identifying and classifying the medical devices connected to your environment is critical and the most common first step.
- To appropriately build your IoMT asset inventory, Asimily’s passive scanning capabilities to create an accurate device profile that includes:
- Operating system
- IP address
- MAC address
- Port numbers
- Applications
- Hostname
- Version number
Further with our platform, HDOs can identify software applications running on the network by inspecting packets rather than initiating traffic to analyze responses for safe, real-time:
- Device behavior analysis
- Risk assessment
- Threat detection
- Remediation
When integrated with the IT team’s active scanning tool, these solutions enable a comprehensive, layer approach to endpoint security that incorporates IoMT into the overarching risk management program. Asimily can augment its passive inventory data gathering with other data sources as well, such as imports of pre-existing inventories.
2. Vulnerability Prioritization
While all IoMT can connect to the public internet, not every device does or does all the time. Further, sometimes the security controls in place make identifying vulnerabilities difficult. For example, It may not be clear what software components and their vulnerabilities are running on a newly installed device.
After detecting these vulnerabilities, you need a solution that has a deep contextual engine to prioritize them according to their exploitability in your unique environment. For example, devices can have different configurations with different risk levels. The same device on a subnet with other devices has less risk than one with 10,000 neighbors to potentially infect. Risk is contextual; the public rating of a vulnerability’s severity is not.
Asimily’s patented engine enables your HTM team to prioritize vulnerabilities by aggregating and analyzing:
- Security data that the manufacturer supplies
- Open-source software components that developers used
- Vulnerability criticality
- Attacker tactics, techniques, and procedures (TTPs) that can use the vulnerability
By aggregating and correlating this data, you can identify and prioritize high-risk devices, ones that attackers are highly likely to exploit that would also have a high impact on your organization and patients if compromised.
3. Remediate Vulnerabilities According to Environment’s Needs
Often, remediating IoMT vulnerabilities is even more difficult than identifying them. Manufacturers no longer support legacy technologies. Meanwhile, many of the hundreds of communication protocols used by devices have not had the same volume of real-world security testing as, like TCP/IP. Vulnerabilities are likely to be present.
When remediating the vulnerabilities in your environment, your HTM or IT team can use Asimily for actionable recommendations that identify activities like:
- Deactivating unneeded services that won’t impact clinical function
- Using a Network Access Control (NAC) tool to block risky ports
- Hardening vulnerable devices by altering their configurations
- Implementing micro-segmentation for devices whose clinical function would be impaired by altering configurations
Ideally, the actionable recommendations are simple, short and effective, not just relying on making network configurations more complex for years to come.
4. Detect IoMT Anomalies to Enhance Incident Response
To reduce data breach impact and cost, HDOs need a way to detect abnormal behavior that can indicate an incident. The earlier that your security teams detect suspicious activity, the faster they can investigate, contain, and eradicate the attacker. For example, by integrating IoMT monitoring with your NAC and firewall policies, your security team can identify medical devices communicating with foreign IP addresses, potentially indicating a connection with a malicious common and control (C2) server.
With Asimily’s purpose-built IoMT security and monitoring solution, your security team builds a comprehensive IoMT security risk management program that enhances your incident response processes with:
- Policy Management: Asimily provides policy management at a granular level, allowing you to set up alerts for specific incidents and tailor their policies based on particular attributes of their network of IoMT devices. This makes it quicker to hone in on unusual activity in your network and greatly reduces incident response times.
- Packet Capture: capture data continuously on an arbitrary or pre-programmed interval to aid investigations, inform security officers accurately, prove due diligence, and rapidly identify a breach.
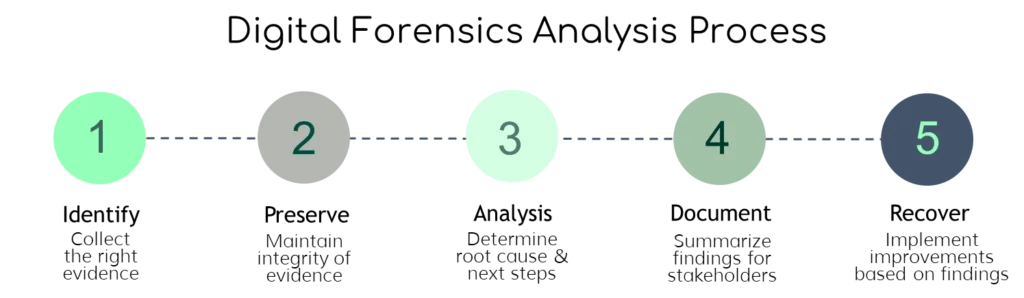
- Forensic Analysis: facilitate and accelerate the investigation process with data collection and analysis that captures raw network traffic, either on command or automatically in response to suspicious activity.
5. Iterate Processes
Vulnerability prioritization and management is a never-ending process. Once you remediate your highest-risk vulnerabilities, you need to work your way through the next set of security weaknesses. To determine next steps, your security team(s) can run a risk simulation on your devices to identify which recommendations, vulnerabilities, and anomalies will mitigate risk as efficiently as possible.
As you continue to iterate your processes, your teams can coordinate during the pre-procurement process by running risk simulations to understand how new devices impact your security profile. Through this process, they can work together to implement new IoMT more securely.
Asimily’s Advanced Vulnerability Prioritization & Management
With Asimily’s patented vulnerability prioritization capabilities, you gain holistic visibility into all medical devices connected to your networks so that your HTM, IT, and security teams can begin working toward a comprehensive security program.
HDOs efficiently identify high-risk vulnerabilities with our proprietary, patented algorithm that cross-references vast amounts of data from resources like Manufacturer Disclosure Statements for Medical Device Security (MDS2s), Software Bills of Material (SBOMs), Common Vulnerability and Exposure (CVE) lists, the MITRE ATT&CK Framework, and NIST Guidelines. It understands your unique environment so that our deep contextual recommendation engine can provide real-time, actionable remediation steps to reduce risk and save time.
By leveraging Asimily’s advanced Vulnerability prioritization and Management and Incident Response capabilities you can mature your IoMT security risk management program. Schedule a consultation with an Asimily expert to see how you can efficiently prioritize and remediate vulnerabilities with the leading IoMT risk management platform.
Secure Every IoT Device.
Automatically.
Cyber threats move fast — so should you. Asimily gives instant inventory and smart, prioritized risk mitigation insights for every IoT, OT, and IoMT device — so you can take action before threats strike.