Safeguarding Smart Traffic Lights: A Top Priority for Smart Cities
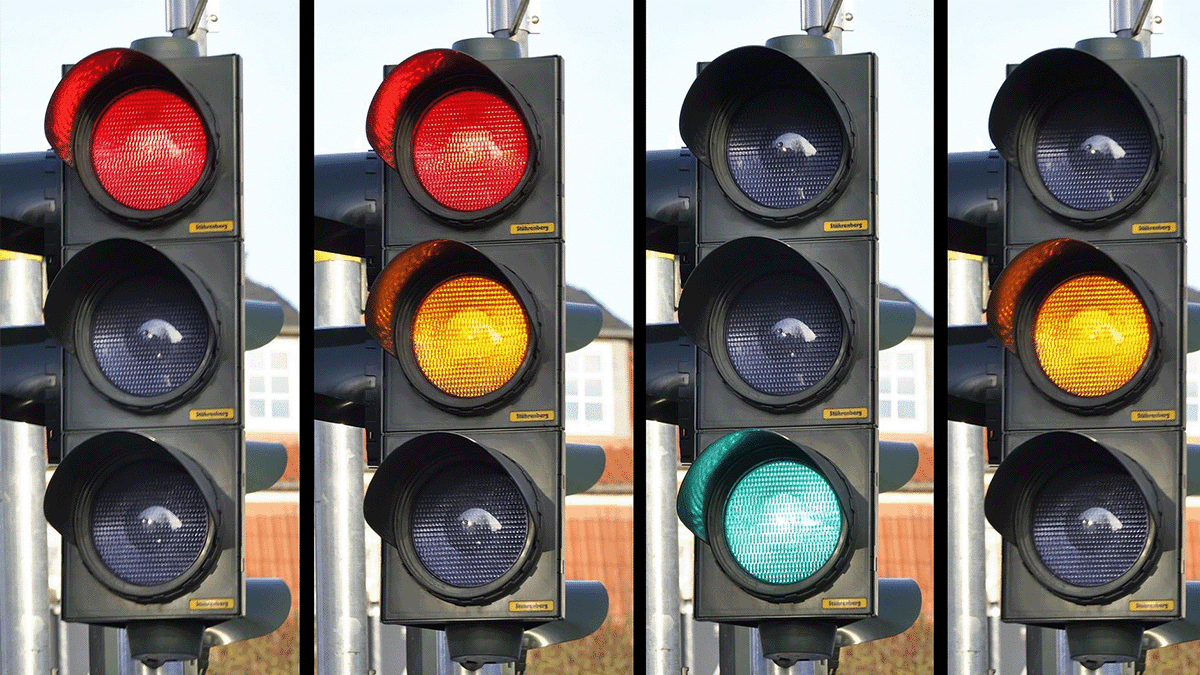
Traffic congestion remains a persistent challenge for urban environments. Increasingly, cities are turning to smart traffic lights to enhance the efficiency of traffic monitoring and management. Smart traffic lights have adaptive traffic management systems that can adjust the flow of traffic, detect approaching emergency vehicles, enhance intersection safety, and more. According to the Federal Highway Administration (FHWA), as many as 75% of the 300,000 traffic signals in the United States could be improved with updates, adjusted timing, or by coordinating adjacent signals.
However, like other Internet of Things (IoT) devices, smart traffic lights can become the target of a cyberattack. In early 2023, over 150,000 traffic light controllers were at risk after a critical vulnerability was discovered in the Econolite EOS traffic control software. Over the past several years, several instances of traffic light hacking have occurred. Some examples include:
- August 2014: Security researchers from the University of Michigan gained control over 100 traffic signals in Michigan City using a single laptop. They observed multiple weaknesses in the system, including unencrypted radio signals, factory-default usernames and passwords, and an open debug port.
- November 2016: The San Francisco Municipal Transportation Agency received a ransom demand for roughly $70,000 in Bitcoin after hackers compromised internal systems. Instead of shutting down the city’s Muni tramway, attackers took fare machines offline, allowing passengers to ride for free.
- August 2020: Security researchers Wesley Neelen and Rik van Duijn found a way to influence traffic lights across the Netherlands. They reverse-engineered an Android app to remotely send spoofed data to connected traffic lights that showed nonexistent bicyclists approaching, changing the light to green.
- June 2023: Olsztyn, Poland, suffered a cyberattack that paralyzed its transit system. The attack hit nearly 100 intersections and halted 20 trains. On August 29, 2023, two suspects were arrested. They allegedly caused the attack by sending “stop” commands via radio frequency. According to a Polish security researcher, the trains used a radio system without encryption or authentication.
Securing smart traffic light systems is critical to protecting smart city infrastructure from cyberattacks, and security teams need to understand the risks associated with these devices.
How Attackers Compromise Smart Traffic Lights
While smart traffic lights can help cities ease congestion and enhance road safety, the internet connectivity of these devices provides threat actors with a multitude of ways to compromise them.
Lack of Encryption
Many traffic light systems lack encryption for firmware or communications channels, making devices vulnerable. Since traffic light sensors don’t authenticate the origin of the data they receive, a threat actor could push a malware-laden firmware update to gain control over the device. Security researcher Cesar Cerrudo built a prototype to test the efficacy of such an attack in 2014, identifying 200,000 vulnerable wireless sensors.
Physical Security Flaws
Typically, a traffic control cabinet or traffic light controller (TLC) cabinet is mounted near intersections and used to manage traffic light commands. Cabinets usually contain a controller, switches, power supply, MMU, and other equipment. If an attacker gained physical access to a TLC, they could change lights from red to green or vice versa, remove fail-safe equipment, or perform other attacks.
Weak Authentication
Smart traffic lights rely on the information they receive to adjust signal timing. Unfortunately, many smart traffic lights fail to authenticate the input they receive, making it possible for attackers to change vehicle prioritization or disrupt the flow of traffic.
Software Vulnerabilities
Critical vulnerabilities in software or firmware remain the most common way for attackers to gain unauthorized access to a device or network. Unfortunately, the longer a vulnerability remains unpatched on a device, the easier it is for threat actors to find and exploit it. For example, a vulnerability impacting SWARCO PU LS4000 traffic light controllers was reported to the vendor in 2019, but a patch and advisory were not released until 2020.
Cybersecurity Best Practices for Smart Traffic Lights
The security of traffic infrastructure is crucial. Traditional security monitoring tools often fail to provide visibility into the IoT device security, and many smart traffic lights lack the robust security controls seen in devices like computers or servers. Cities should implement comprehensive cybersecurity measures to protect these critical systems from cyberattacks.
Inventory Devices
Smart traffic infrastructure is more than just traffic lights. Cities need to know how many sensors, pedestrian buttons, webcams, TLCs, or other devices exist at each intersection.
An important first step in ensuring all devices are secure is to inventory every device connected to the network—commonly called an attack surface. A passive scanner can detect and fingerprint these technologies with information including:
- Hardware: manufacturer, model, serial number
- Software: operating system, version, firmware revisions
- Device type and function
- Security assessment: vulnerabilities and risks
Passive scanning (gaining information from listening to network traffic only) is the safest starting point, as many IoT devices do not respond well to standard (active) security scanning.
Monitor for Anomalous Behavior
Connected traffic lights should only communicate with known IP addresses in well-understood ways. Early detection of anomalous behavior can enhance a security team’s ability to respond to an in-progress attack. For traffic lights, this may include communicating with unknown IP addresses or sudden firmware or configuration changes. Even in the case of malware introduced via physical access, anomalous behaviors may still be detectable.
Enhance Detection and Investigation
Cyberattacks can originate from anywhere in the network. Incorporating IoT devices into security monitoring tools can enhance attack detection and investigation. When security teams receive high-fidelity alerts that cover the totality of a network, they can detect attacks faster and make better decisions, potentially mitigating the severity of a cyberattack.
When organizations employ solutions that can capture network packet data, security analysts obtain important forensic data needed to determine root causes including:
- RAM from servers (important for fileless malware, which doesn’t touch magnetic media)
- Traffic information from network devices
- Data transferred to an FTP server
How Asimily Helps Defend Connected Traffic Lights
Asimily is designed with IoT devices in mind, monitoring network traffic to and from IoT devices, such as smart traffic lights, and sending alerts based on anomalous behavior that might indicate an attack.
Our risk scoring provides information on high-risk vulnerabilities, while our proprietary algorithm leverages vast amounts of data from resources like EPSS (Exploit Prediction Scoring System), Software Bills of Material (SBOMs), Common Vulnerability and Exposure (CVE) lists, the MITRE ATT&CK Framework, and NIST Guidelines. It understands your unique environment, so our deep contextual recommendation engine can provide the most efficient actionable remediation steps to reduce risk and save time.
Asimily’s recommendations can easily be applied in several ways, including through seamless integration with NACs, firewalls, or other network enforcement solutions.
To learn more about Asimily, download our whitepaper, IoT Device Security in 2024: The High Cost of Doing Nothing, or contact us today.
Secure Every IoT Device.
Automatically.
Cyber threats move fast — so should you. Asimily gives instant inventory and smart, prioritized risk mitigation insights for every IoT, OT, and IoMT device — so you can take action before threats strike.