Most Notable Healthcare Cyberattacks of 2023 and Their Impact on Patient Safety
Modern healthcare delivery organizations (HDOs) incorporate more Internet of Things (IoT) devices as they seek to provide best-in-class patient care. However, cybercriminals continue to target the industry and its patients, looking for any opportunity to make money. Unlike other organizations, HDOs face intense government scrutiny under the Health Insurance Portability and Accountability Act (HIPAA), meaning that information about their security is often publicly available. For example, according to the US Department of Health and Human Services (HHS) Office for Civil Rights (OCR), the agency investigated 309 healthcare cyberattacks between January 1, 2023 and December 31, 2023, with these events impacting 3,7070,919 patients.
As threat actors continue to barrage the healthcare industry, HDOs should understand how attackers can leverage this expanded attack surface to their advantage and identify solutions that reduce a data breach’s impact.
A Tale of Four Healthcare Breaches
For healthcare organizations, security incidents often undermine patient care and trust. The most notable healthcare cyberattacks of 2023 highlight the way that attacks against these highly connected systems can impact patients personally by leaving them without access to proper care and giving attackers the ability to target them individually.
Fred Hutchinson Cancer Center, December 2023
On December 14, 2023, plaintiffs filed a class action lawsuit against Fred Hutchinson Cancer Center alleging that unauthorized access to protected health information (PHI) allowed attackers to send threatening emails. According to the allegations, the emails claimed that cybercriminals had data for more than 800,000 patients including:
- Names
- Social security numbers
- Medical history
Further, the complaint alleges that each email requested $50 from the patient to have the information scrubbed from the dark web. According to the court document, at least 300 current and former patients reported receiving one of these emails.
McLaren Health Care, November 2023
Cybercriminal gang BlackCat deployed a ransomware attack against the HDO in August 2023, stealing sensitive personal health information of 2.5 million patients. Although no one knows the actual number and identities of affected patients, McLaren reported that it was investigating reports of cybercriminals making patient data available on the dark web.
Beyond the impact on patient data, the HDO also took its computer network offline while investigating the incident, disrupting patient care across its facilities, which also includes one of Michigan’s largest networks of cancer centers and providers.
HCA Healthcare, July 2023
Cybercriminals stole patient data from an external storage location that HCA Healthcare used to automate email message formatting. The HDO discovered the exposure of approximately 11 million patient records across 27 million rows of data when cybercriminals released it on an online platform. The data that these attackers stole included the following information:
- Patient name
- City
- State
- Zip code
- Email address
- Telephone number
- Date of birth
- Gender
- Service date
- Date of next appointment
Within a week, affected parties filed a class action lawsuit alleging that HCA Healthcare violated its obligations under the FTC Act, HIPAA, and contract law. The lawsuit requests a jury by trial, looking to recover damages, plaintiffs’ legal expenses, implementation of additional security controls, and engagement of third-party penetration testing and security auditors.
Sutter Health, May 2023
Sutter Health’s third-party contractor Welltok, Inc used the MOVEit file transfer program. On May 30, 2023, attackers accessed the vendor’s systems, stealing patient PHI that included:
- Names
- Dates of birth
- Health insurance information
- Provider names
- Treatment cost information
- Treatment information
- Diagnoses
Since Welltok failed to notify patients until late October 2023, both companies have been sued in the state of California for potentially violating state and federal laws. Depending on the outcome, victims may be entitled to monetary damages of $1000 per violation.
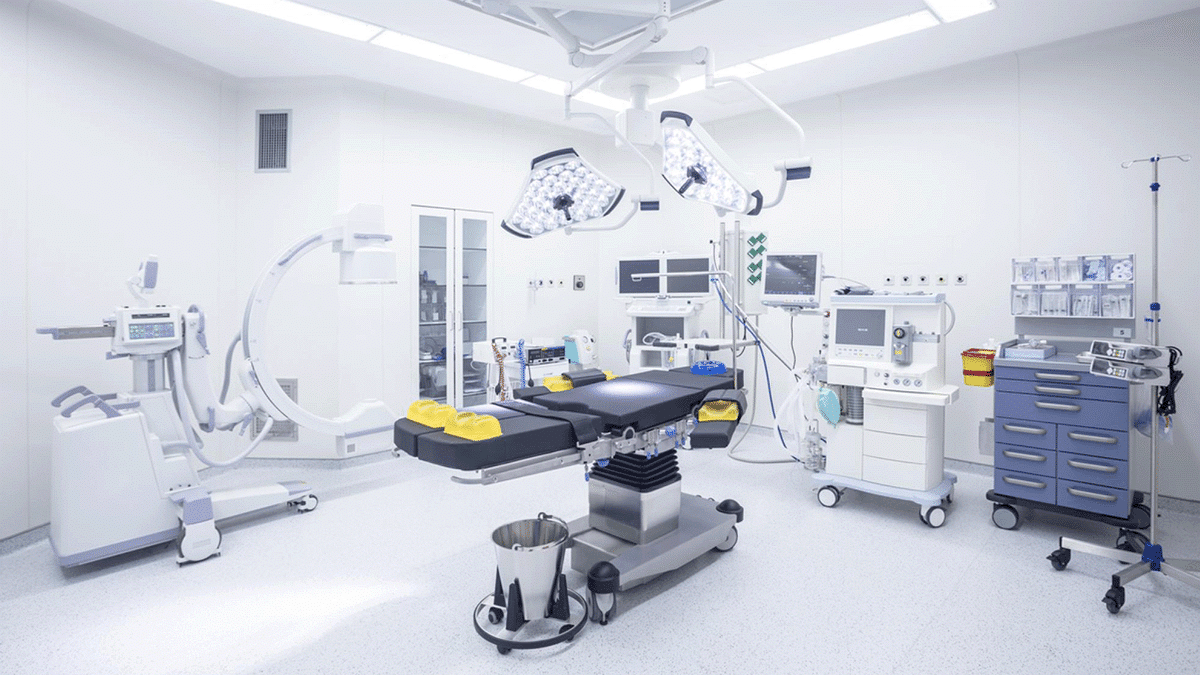
Mitigating Data Breach Risks by Securing IoT Devices
In light of the potential for HIPAA fines and increased regulatory data protection oversight, HDOs need solutions that enable them to build holistic programs across all devices that threat actors can use to achieve their attack objectives.
Create an IoT Asset Inventory
Incorporating IoT devices into your security program is critical. The first step is to identify and categorize them as part of your asset inventory. However, since traditional IT tools can take them offline, HDOs need a passive scanning solution that inspects packets rather than initiating traffic. Any chosen solution should provide the following information about each connected device:
- Manufacturer
- Model
- Operating systems and versions
- Software and versions
- Applications
- IP address
- MAC address
- Port numbers
- Hostname
Identify Vulnerabilities
Any vulnerability can give attackers a way to access your networks and systems. While on the IT side, you may be able to identify a known vulnerability like MOVEit, you still need a solution that mitigates risk for your IoT fleet while integrating with your other vulnerability monitoring tool data.
As you bring these devices into your overarching vulnerability management program more purposefully, you need a solution that aggregates and analyzes IoT vulnerability data, including:
- Manufacturer-supplied security data
- Open-source software components
- Vulnerability criticality
- Current attack methods using the vulnerability
Additionally, this solution should also provide simple, short, and effective remediation suggestions to make securing your IoT fleets easier. Some examples of alternative clinically validated methods might include:
- Deactivating unnecessary services without impacting critical function.
- Blocking risky services with a Network Access Control (NAC) tool.
- Hardening vulnerable devices by updating their configurations.
- Implementing micro-segmenting when altering configurations affects the device operations
Monitor for Abnormal Activity
Threat actors can use any asset connected to your network as part of their attack. Even if they gain access using a traditional IT asset, they can still use an IoT device as part of lateral movement or escalation of privileges.
Your security monitoring should include IoT devices by establishing a baseline of normal behavior so that your security team can identify abnormal activity that might indicate attackers misusing them. When security teams incorporate this data, they can build high-fidelity alerts that enable them to more rapidly detect attacks, reducing impact.
Collect Forensic Data
If you experience a security incident, you need to have forensic data available to provide answers to regulatory and law enforcement agencies. By incorporating IoT into your forensic data capture, you can correlate and analyze it with other information, including:
- RAM information from servers
- Traffic information from network devices
- Data transferred to an FTP server
Report to Leadership and Board of Directors
Senior leadership teams and boards of directors need the appropriate visibility into their security risk. They need the right combination of technical data with visualizations that provide insights into trends. Your senior leadership team and directors need high-level insights that include:
- Trends over time
- Number of devices categorized as high-impact and high-risk
- Vulnerabilities remediated within a specified time period
- Categories of anomalous behavior and technical risks
When armed with this type of information, these stakeholders can make informed decisions about current security posture and future investments.
Asimily: Reduce Data Breach Likelihood and Impact
Asimily provides holistic context into an HDO’s environment when calculating Likelihood-based risk scoring for devices. Our vulnerability scoring considers the compensating controls so you can more appropriately prioritize remediation activities.
HDOs efficiently identify high-risk vulnerabilities with our proprietary, patented algorithm that cross-references vast amounts of data from resources like EPSS, Manufacturer Disclosure Statements for Medical Device Security (MDS2s), Software Bills of Materials (SBOMs), Common Vulnerability and Exposure (CVE) lists, the MITRE ATT&CK Framework, and NIST Guidelines. It understands your unique environment, so our deep contextual recommendation engine can provide real-time, actionable remediation steps to reduce risk and save time.
Asimily clients are 10x more efficient because the engine can pinpoint and prioritize the top 2% of problem devices that are High-Risk (High Likelihood of exploitation and High Impact if compromised). Asimily’s clinically validated recommendations can easily be applied in several ways, including through seamless integration with NACs, firewalls, or other network enforcement solutions.
To learn more about Asimily, download our IoT Device Security in 2024: The High Cost of Doing Nothing whitepaper or contact us today.
Reduce Vulnerabilities 10x Faster with Half the Resources
Find out how our innovative risk remediation platform can help keep your organization’s resources safe, users protected, and IoT and IoMT assets secure.