Securing Healthcare: Mitigating Vulnerabilities in Infusion Pumps
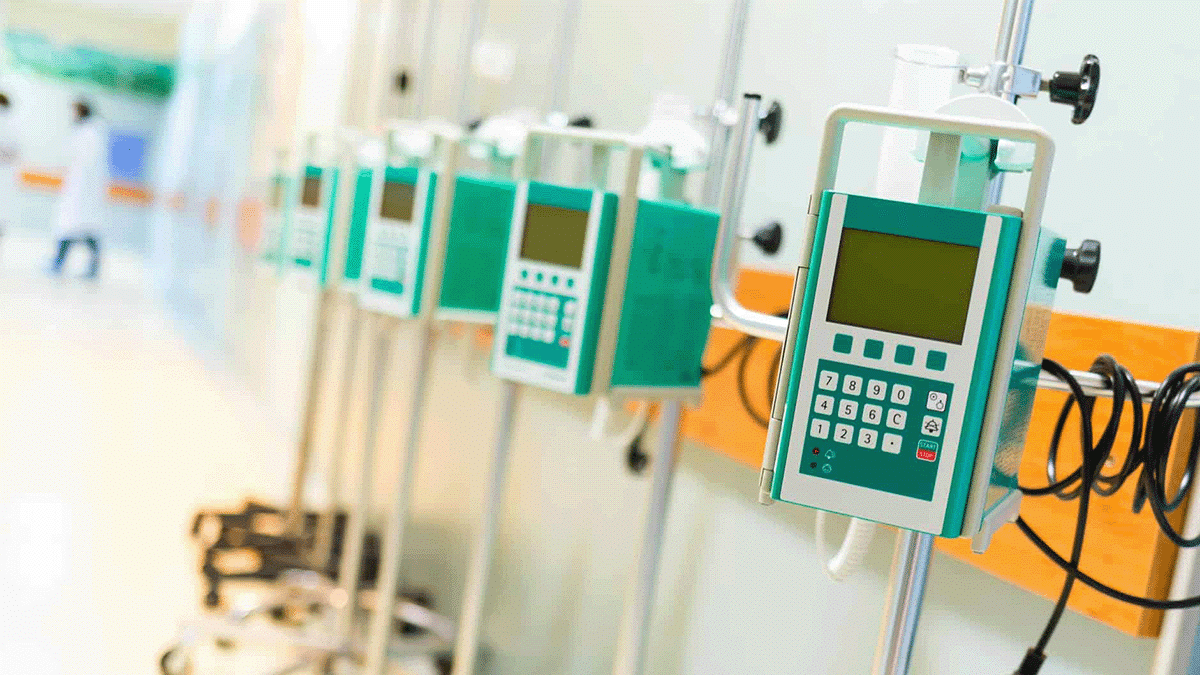
Infusion pumps control the delivery of medication or nutrients into a patient’s body. They are commonplace in hospitals, clinics, nursing facilities, and homes. Infusion pumps provide additional enhancements, such as sending alerts for adverse drug interactions or if a user sets the pump parameters outside recommended safety limits. However, IoT medical devices like these smart pumps also carry increased cybersecurity risks.
Healthcare organizations have long been prime targets for threat actors. They hold a wealth of sensitive patient data, and many struggle to stay on top of cybersecurity best practices to secure IoT devices such as infusion pumps. Infusion pumps account for 38% of a hospital’s Internet of Things (IoT) footprint and as many as 75% of infusion pumps connected to hospital networks may be vulnerable to digital attacks, according to a recent cybersecurity scientific research report.
Over the last several years, there has been an uptick in vulnerabilities and manufacturer recalls impacting IoT infusion pumps, all posing serious risks to patients. Some examples include:
- July 2023: Becton Dickinson disclosed eight vulnerabilities in its Alaris infusion pump system, including one high-risk vulnerability. The vulnerabilities allowed a threat actor to compromise sensitive data, modify firmware, or change the system configuration.
- December 2022: Becton Dickinson disclosed a vulnerability impacting BodyGuard Pumps. A threat actor could change configuration settings or disable the pump by exploiting the vulnerability.
- March 2022: Baxter Healthcare recalled its SIGMA Spectrum Infusion Pump. Later, the FDA announced a Class I recall of the Baxter Sigma Spectrum infusion pumps due to a defective alarm that resulted in three deaths and 51 serious injuries.
- August 2021: Cybersecurity research firm Trellix discovered five vulnerabilities impacting B. Braun infusion pumps. The vulnerabilities allowed a threat actor to modify a pump’s configuration and potentially alert medication dosage.
Securing IoT infusion pumps is critical, but even when patches for vulnerabilities are available, some organizations may fail to apply them in a timely manner.
Healthcare Organizations Face Challenges Securing Infusion Pumps
A large hospital or medical facility may have thousands of infusion pumps. This makes it especially challenging for personnel to identify, remove, or patch every vulnerable device according to the manufacturer’s instructions. They are favorite targets for well-meaning healthcare providers to surreptitiously stash nearby – such as in a closet – so they are available for use, but sometimes unavailable for inventory or security updates in the interim when they can’t be found.
Research from the Ponemon Institute showed that 53% of healthcare organizations were concerned about insecure medical devices. These concerns are well-founded, considering that there are an average of 6.2 vulnerabilities per medical device, with recalls issued for critical devices and more than 40 percent of medical devices at the end-of-life stage, offering little to no security patches or upgrades.
Patching medical devices is a complex, slow process, even when patches are available. The healthcare industry is highly regulated and has a low tolerance for operational downtime, as it presents a direct risk to patient safety. Further compounding the problem, a cybersecurity skills shortage has resulted in more than 4 million unfilled openings. According to Ponemon, over half of healthcare organizations reported a lack of in-house cybersecurity expertise in 2023, a 53% increase from 2022.
The longer a vulnerability remains unpatched on a device, the easier it is for threat actors to find and exploit it. In 2023, vulnerability exploitation nearly tripled as a means for attackers to gain initial access to a network. IoT devices with unpatched vulnerabilities can leave healthcare organizations at risk of experiencing a cyberattack, including ransomware, which can significantly impact patient care.
Cybersecurity Best Practices for Infusion Pumps
All healthcare organizations that use IoT infusion pumps should consider the associated cybersecurity risks and how to mitigate them.
Inventory Devices and Take Regular Audits
Connected infusion pumps are not the only risk. Healthcare organizations have a multitude of IoT devices that provide critical patient care and require protection from cyber attacks. An important first step in ensuring all devices are secure is to create an inventory of every device connected to the network—this is commonly referred to as an attack surface.
Organizations should consider using a passive scanner that can detect and fingerprint these technologies with information including:
- Hardware: manufacturer, model, serial number
- Software: operating system, version, firmware revisions
- Device type and function
Passive scanning (gaining information from listening to network traffic only) is the safest starting point, as many IoT do not respond well to standard (active) security scanning. As a best practice, conduct regular audits to update the inventory.
Identify and Remediate Vulnerabilities
Once an organization understands the totality of its attack surface, it can determine if any of the devices on the network have vulnerabilities that require remediation. Passive scanners can provide several useful insights about the vulnerabilities that attackers are most likely to exploit:
- Exploitable vulnerabilities within the environment
- Exploitable vulnerabilities for each specific device
- Provide guidance for patching based on exploitability
- Mitigation recommendations specific to the device, such as applying security updates or using compensating controls for IoT devices
Monitor for Anomalous Behavior
All devices on a network should only communicate with known IP addresses in well-understood ways. Early detection of anomalous behavior can enhance a security team’s ability to respond to an in-progress attack. For infusion pumps, this may include communicating with unknown IP addresses or sudden configuration changes.
Enhance Detection and Investigation
Cyber attacks can originate from anywhere within a network. Incorporating IoT devices into security monitoring tools can enhance attack detection and investigation. When security teams receive high-fidelity alerts that cover the totality of a network, they can detect attacks faster and make better decisions, potentially mitigating the severity of a cyberattack.
When organizations employ solutions that can capture network packet data, security analysts obtain important forensic data needed to determine root cause such as:
- RAM from servers (important for fileless malware, which doesn’t touch magnetic media)
- Traffic information from network devices
- Data transferred to an FTP server
Asimily: Infusion Pump Monitoring
Asimily is designed with IoT devices in mind, monitoring traffic to and from IoT devices, including infusion pumps.
Our vulnerability scoring provides information on high-risk weaknesses, while our proprietary algorithm that leverages vast amounts of data from resources like EPSS (Exploit Prediction Scoring System), Software Bills of Material (SBOMs), Common Vulnerability and Exposure (CVE) lists, the MITRE ATT&CK Framework, and NIST Guidelines. It understands your unique environment, so our deep contextual recommendation engine can provide real-time, actionable remediation steps to reduce risk and save time.
Asimily’s recommendations can easily be applied in several ways, including through seamless integration with NACs, firewalls, or other network enforcement solutions.
To learn more about Asimily, download our whitepaper, IoT Device Security in 2024: The High Cost of Doing Nothing, or contact us today.
Secure Every IoT Device.
Automatically.
Cyber threats move fast — so should you. Asimily gives instant inventory and smart, prioritized risk mitigation insights for every IoT, OT, and IoMT device — so you can take action before threats strike.




