Medical Device Vulnerability Management
Last updated: May 2026
The average connected medical device carries 6.2 vulnerabilities, and 99% of hospitals manage at least one device with a known exploited vulnerability. At the same time, 60% of medical devices in active clinical use are end-of-life with no available security patches. For healthcare security teams, the question is not whether medical devices have vulnerabilities. They do. The question is how to determine which ones actually put patients and data at risk, and what to do about the ones you cannot patch. Medical device vulnerability management is the discipline that answers both questions. This guide covers the full lifecycle of medical device vulnerability management, from discovery and assessment through prioritization, remediation, compensating controls, and ongoing monitoring, with specific attention to the constraints that make healthcare different from every other industry.
On this page:
- What Is Medical Device Vulnerability Management?
- Why Medical Devices Require a Different Approach
- The Medical Device Vulnerability Management Lifecycle
- Vulnerability Discovery for Medical Devices
- Risk-Based Vulnerability Prioritization
- Remediation and Compensating Controls
- Ongoing Monitoring and Configuration Management
- Regulatory Requirements
- Common Pitfalls in Medical Device Vulnerability Programs
- How Asimily Supports Medical Device Vulnerability Management
What Is Medical Device Vulnerability Management?
Medical device vulnerability management is the process of identifying, assessing, prioritizing, and mitigating security weaknesses in connected medical devices to protect patient safety, clinical operations, and sensitive health data. It covers vulnerabilities in device firmware, operating systems, software applications, communication protocols, and configuration settings.
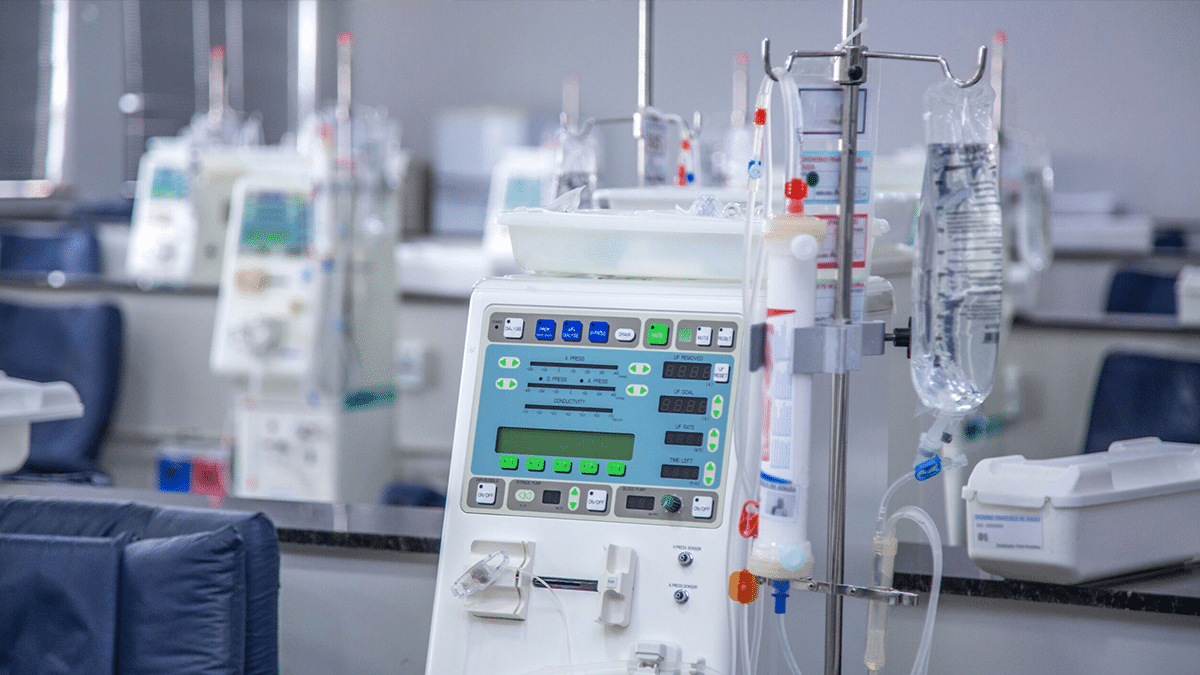
This process applies to the full range of connected medical devices in a healthcare delivery organization: infusion pumps, patient monitors, imaging systems (MRI, CT, ultrasound), medication dispensing cabinets, ventilators, laboratory instruments, and the clinical workstations and servers that support them. It extends to the programming stations and remote monitoring infrastructure for implantable devices like pacemakers and neurostimulators.
Medical device vulnerability management is distinct from general IT vulnerability management because the devices operate under constraints that IT endpoints do not share: they often cannot be patched without vendor coordination, they may require scheduled maintenance windows, active scanning can disrupt them, and taking them offline for remediation can directly affect patient care.
The scale of the problem is significant. Research across 2.25 million IoMT devices found an average of 6.2 vulnerabilities per device. Forescout’s 2026 research identified medication dispensing systems, medical image printers, DICOM gateways, MRI scanners, and healthcare workstations as the riskiest IoMT device categories. The RunSafe Security 2026 Medical Device Cybersecurity Index found that 24% of healthcare facilities have experienced a cyberattack on a medical device, with 80% of those reporting moderate or significant disruption to patient care.
Related: IoT Security: The Complete Guide to Protecting Connected Devices
Why Medical Devices Require a Different Approach
Security teams accustomed to managing IT vulnerabilities often underestimate how different medical device vulnerability management is in practice. Four factors shape every decision:
Patient safety is the primary constraint. In IT, patching a vulnerable server causes a brief outage. In healthcare, patching a ventilator or infusion pump may require coordinating with clinical staff, ensuring backup equipment is available, and scheduling around patient care schedules. A poorly timed update can directly affect treatment delivery. Every vulnerability management decision in healthcare must weigh cybersecurity risk against patient safety impact.
Patching is rarely straightforward. IT devices accept automated patches on weekly or monthly cycles. Medical devices may require vendor-specific update procedures, compatibility testing against other systems in the clinical workflow, and validation that the update does not alter device performance in ways that affect safety. Some patches require FDA clearance before deployment. Some void manufacturer warranties. Some devices have reached end-of-life and will never receive another patch. The 2025 Verizon DBIR recorded a 34% year-over-year increase in successful vulnerability exploits across all industries, but healthcare teams frequently cannot remediate on the timelines the vulnerability severity demands.
Active scanning causes harm. Traditional vulnerability scanners send probes to devices that can crash medical equipment, disrupt clinical workflows, and create patient safety incidents. Vulnerability assessment for medical devices must rely on passive identification, correlating observed device attributes (manufacturer, model, firmware version) with vulnerability databases, without sending traffic to the device.
Regulatory requirements add complexity. HIPAA, FDA Section 524B, state mandates like New York’s 10 NYCRR 405.46 and the Texas HHSC directive, and the 2026 HIPAA Security Rule update all impose requirements on how medical device vulnerabilities are managed. These regulations increasingly expect documented vulnerability management programs, not ad hoc responses to individual advisories.
Related: Medical Device Security Standards: What HDOs Need to Know
The Medical Device Vulnerability Management Lifecycle
Effective medical device vulnerability management follows a continuous lifecycle rather than a reactive, advisory-by-advisory approach:
Discover every connected medical device and build a comprehensive inventory including manufacturer, model, firmware version, operating system, communication patterns, and clinical function.
Assess each device’s vulnerability exposure by correlating its attributes against CVE databases, EPSS scoring, manufacturer advisories, SBOMs, and FDA safety communications.
Prioritize vulnerabilities based on contextual risk: exploit availability, network exposure, device criticality, patient safety implications, and existing compensating controls.
Remediate through the most efficient available method: firmware patching where possible, compensating controls where patching is not feasible.
Monitor continuously for new vulnerabilities affecting devices in your inventory, configuration drift from approved baselines, and anomalous device behavior that could indicate compromise.
Report vulnerability management activity and risk posture to leadership, auditors, and regulators in a format that demonstrates program maturity.
This lifecycle must run continuously, not quarterly. New CVEs are published daily, device populations change as equipment is added, moved, or decommissioned, and the threat environment evolves.
Vulnerability Discovery for Medical Devices
Medical device vulnerability discovery has two components: knowing what devices you have, and knowing what vulnerabilities affect them.
Device Inventory
You cannot assess vulnerabilities on devices you do not know are on your network. Healthcare environments routinely discover 15-30% more connected devices than expected once proper discovery tools are deployed. Clinical engineering adds devices. Vendors install monitoring equipment. Departments procure equipment independently. Each one expands the vulnerability surface.
Discovery must be passive. Asimily’s passive deep packet inspection identifies and classifies medical devices by observing their network traffic, without sending any packets that could disrupt clinical operations. The platform covers clinical protocols (HL7, DICOM) alongside standard IT traffic. When a new device type appears, rapid protocol analysis allows classification without waiting for a product release cycle.
Vulnerability Correlation
Once devices are inventoried with their specific attributes (manufacturer, model, firmware version, OS), those attributes are correlated against multiple vulnerability data sources: the National Vulnerability Database (NVD) and CVE lists, Exploit Prediction Scoring System (EPSS) scores that estimate the probability of exploitation within 30 days, Software Bills of Materials (SBOMs) that identify third-party components with their own vulnerability histories, manufacturer security advisories and patch notifications, and FDA safety communications and recalls. 81% of healthcare organizations now rate SBOMs as “important” or “essential” for medical device security, and 35% will not consider a device without one.
The SBOM component deserves particular attention. A medical device may appear free of vulnerabilities based on its primary software, but may contain third-party libraries or embedded components with critical CVEs. The Log4j vulnerability in 2021 demonstrated how a single third-party component could affect tens of thousands of products across industries. Without SBOM data, security teams have no visibility into these embedded risks. FDA Section 524B now requires manufacturers to provide SBOMs for new device submissions, but the majority of devices currently in clinical use predate this requirement and lack SBOM documentation entirely. For these devices, vulnerability correlation must rely on observed device behavior and firmware analysis rather than manufacturer-provided component lists.
Asimily automates this correlation across its device inventory, matching each device’s specific firmware version and software components against known vulnerabilities and flagging devices affected by FDA safety communications. This eliminates the manual process of reading each advisory and trying to determine which devices in your environment are affected.
Related: Continuous IoT Vulnerability Detection
Related: FDA Recalls and Security Advisories
Risk-Based Vulnerability Prioritization
A large health system might have tens of thousands of medical devices carrying hundreds of thousands of CVEs. Addressing every vulnerability equally is not feasible and does not meaningfully reduce clinical risk.
Why CVSS Alone Fails for Medical Devices
CVSS scores measure the theoretical severity of a vulnerability in isolation. They do not account for whether the device is reachable from the internet, whether a known exploit exists, what compensating controls are already in place, or what the clinical impact would be if the device were taken offline for remediation. A critical CVSS score on a device sitting on an isolated clinical VLAN with no known public exploit carries far less actual risk than a medium-severity vulnerability on an internet-facing imaging system with a published proof-of-concept.
Contextual Prioritization
Effective medical device vulnerability management requires analysis that factors in exploit availability (is there a known exploit in the wild, and what does EPSS say about exploitation probability?), network exposure (is the device reachable from the internet, from other compromised zones, or only from a segmented clinical network?), device criticality (what is the patient safety impact if this device is compromised or taken offline?), and compensating controls (is the device already behind a segmentation policy that blocks the relevant attack path?).
Asimily’s prioritization combines analysis from Asimily Labs, AI/ML techniques, and the MITRE ATT&CK framework for actual attack path analysis. Rather than using MITRE ATT&CK only for classification, the platform determines whether a vulnerability on a specific device in a specific network context is realistically exploitable. This approach reduces the list of devices requiring immediate action by an order of magnitude, letting security and biomed teams focus effort where it reduces the most clinical risk.
Related: Risk-based IoT Vulnerability Prioritization
Related: Vulnerability Prioritization for IoMT Security
Remediation and Compensating Controls
Once vulnerabilities are prioritized, the next step is determining the most efficient remediation path for each one. In medical device environments, patching is often not the fastest or safest option.
When Patching Is Available
When a manufacturer has released a patch, and the device supports it, patching is the preferred remediation. But even with available patches, healthcare teams must validate compatibility with other systems in the clinical workflow, schedule a maintenance window that minimizes care disruption, coordinate with clinical staff to ensure backup equipment is available, test the patch on a non-production device if possible, and document the update for regulatory compliance.
Asimily tracks patch availability for devices in its inventory and provides specific instructions for applying updates. The platform also models the risk impact of the patch, allowing teams to verify that the update actually reduces the vulnerability exposure for that device in its network context.
When Patching Is Not Feasible
For the 60% of medical devices that are end-of-life, and for many others where patching timelines stretch weeks or months, compensating controls must bridge the gap:
Network segmentation restricts what a vulnerable device can communicate with, containing the blast radius if it is compromised. Asimily’s targeted segmentation groups devices by exploit vector using the MITRE ATT&CK framework, blocking specific attack paths at the network level. The Policy Simulation feature lets teams preview effects before enforcement, reducing the risk of clinical disruption.
Virtual patching blocks known exploitation techniques at the network layer without modifying the device itself.
Configuration hardening removes unnecessary services, closes unused ports, and tightens access controls within whatever management capabilities the device provides.
Asimily prescribes the most efficient compensating control for each vulnerable device and provides specific implementation instructions ranked by effort and impact. The Risk Simulator models the impact of remediation actions before deployment, giving teams confidence that a change will improve security without disrupting patient care.
Related: Maximize Uptime and Minimize Vulnerabilities with Automated IoT Patching
Related: Network Segmentation and Microsegmentation Solutions
Ongoing Monitoring and Configuration Management
Medical device vulnerability management does not end after a patch or compensating control is applied. The vulnerability surface changes constantly as new CVEs are published, device populations change, and configurations drift.
New vulnerability monitoring should be continuous and automated. When a new CVE is published that affects a device in your inventory, the platform should flag it immediately, not wait for a quarterly review. When the FDA issues a safety communication or recall, affected devices should be identified automatically.
Configuration drift detection catches changes to device settings that could reintroduce vulnerabilities. Firmware updates, operational modifications, and manual adjustments can all alter a device’s security posture. Asimily’s Configuration Control capability tracks device configurations over time, detects drift from approved baselines, and alerts when changes occur.
Behavioral monitoring identifies compromised devices through traffic analysis. A medical device that begins communicating with an unfamiliar external IP, transferring unusual data volumes, or using protocols it has never used before may indicate a compromise that exploited an unpatched vulnerability. This is particularly important for end-of-life devices where no patch will ever be available. Behavioral monitoring serves as the last line of defense for permanently vulnerable devices, catching exploitation attempts that compensating controls did not block. Asimily provides continuous behavioral monitoring with packet capture for forensic analysis, and supports custom detection rules that security teams can build without programming to encode organization-specific logic.
Related: Configuration Control
Related: Incident Response Readiness with Packet Capture
Regulatory Requirements
Medical device vulnerability management is increasingly a regulatory expectation, not a discretionary best practice:
HIPAA Security Rule (2026 Update) tightens requirements for access controls, audit logging, and connected device security. Compliance is expected to require demonstrable vulnerability management programs.
FDA Section 524B requires manufacturers to build cybersecurity into the device lifecycle, including SBOMs and vulnerability management plans. 84% of healthcare organizations now include cybersecurity requirements in vendor RFPs, and 35% will not consider a device without an SBOM.
New York 10 NYCRR 405.46 is the first state-level hospital cybersecurity mandate, requiring healthcare facilities to implement cybersecurity programs with specific provisions for connected device security.
Texas HHSC Directive (March 2026) requires Texas healthcare facilities to review their connected medical device security posture.
HHS Cybersecurity Performance Goals establish voluntary but increasingly referenced benchmarks that include medical device vulnerability management as a core expectation.
Organizations with documented, operational vulnerability management programs will be better positioned for compliance audits, cyber insurance renewals, and regulatory examinations.
Related: How Asimily Helps You Comply With the 2026 HIPAA Security Rule Changes
Related: New York’s Hospital Cybersecurity Regulation (10 NYCRR 405.46)
Common Pitfalls in Medical Device Vulnerability Programs
Treating every CVE equally. Without contextual prioritization, teams spend time on low-risk findings while exploitable vulnerabilities on critical devices go unaddressed. Volume does not equal risk.
Relying on CVSS alone. CVSS measures theoretical severity, not actual risk in your specific environment. Two devices with the same critical CVSS score can have completely different real-world risk profiles depending on their network position and compensating controls.
Waiting for patches as the only remediation. Many medical devices will never be patched. A vulnerability management program that depends on patching alone will leave large portions of the device fleet permanently exposed.
Running vulnerability management as a periodic project. Annual or quarterly vulnerability scans produce stale data in environments where device populations and threat intelligence change daily. Medical device vulnerability management must be continuous and automated.
Ignoring pre-purchase assessment. By the time a vulnerable device is discovered on the network, it is already contributing to risk. Evaluating device security before procurement prevents the introduction of known vulnerabilities. Asimily’s ProSecure database provides pre-purchase security risk profiles for medical devices.
Operating in silos. Effective medical device vulnerability management requires collaboration between IT security, clinical engineering (HTM), and procurement. Programs that live entirely within one team miss the context that the others provide. IT security understands CVEs and network threats, but may not know which devices are critical to patient care. HTM understands device function and clinical workflows, but may not track vulnerability intelligence. Procurement controls what devices enter the environment, but may not evaluate cybersecurity posture during purchase decisions. The most effective programs create shared workflows where all three teams contribute to vulnerability assessment and remediation decisions.
Failing to account for clinical context during remediation. A vulnerability management platform that recommends rebooting a ventilator during active use or patching an imaging system during a scheduled procedure is not built for healthcare. Remediation recommendations must account for clinical schedules, device utilization patterns, and the availability of backup equipment. Asimily’s utilization data helps teams identify maintenance windows where remediation is least likely to disrupt patient care.
Related: How HTM Can Work with Cybersecurity to Defend Healthcare
Related: CISO’s Security Risk Assessment Guide for Medical Device Procurement
How Asimily Supports Medical Device Vulnerability Management
Asimily provides the full set of capabilities that medical device vulnerability management requires: passive device discovery across IoMT, IoT, OT, and IT environments, automated vulnerability correlation against CVE databases, EPSS, SBOMs, manufacturer advisories, and FDA safety communications, contextual prioritization using MITRE ATT&CK-based attack path analysis, prescriptive remediation with specific instructions ranked by effort and impact, automated segmentation policy generation with simulation, configuration drift detection, continuous behavioral monitoring, and forensic packet capture for incident response.
The platform integrates with existing network infrastructure, including Cisco ISE and other NAC platforms, firewalls, SIEM, SOAR, and CMDB systems. Asimily customers are able to pinpoint the top 1% of high-risk devices, the ones with both a high likelihood of exploitation and a high impact if compromised, making security and biomed teams significantly more efficient.
Talk to an Asimily Healthcare Security Expert
See How Asimily Protects Healthcare Organizations
Asimily is the next-generation cyber asset and exposure management platform for IT, IoT, OT, and IoMT environments. Learn more about our platform.
Secure Every IoT Device.
Automatically.
Cyber threats move fast — so should you. Asimily gives instant inventory and smart, prioritized risk mitigation insights for every IoT, OT, and IoMT device — so you can take action before threats strike.




