5 Strategies for Effective Medical Device Patching in Hospitals
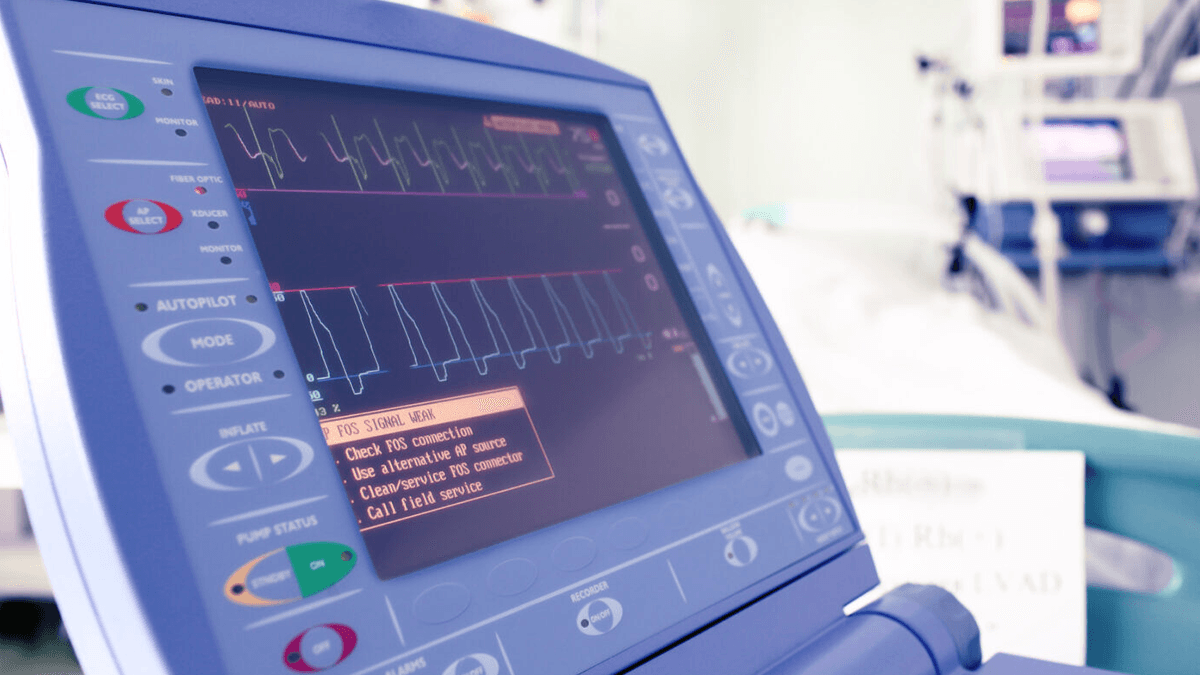
Hospitals and medical staff have a responsibility to protect sensitive patient information while also offering efficient care for those patients. Medical devices form an integral part of improving the performance of modern healthcare, but they present unique security challenges that can put patients and the hospital at risk if left unaddressed.
Neglecting critical software updates and medical device patching for those devices could lead to data theft, ransomware attacks, device failure, and legal liability, among other serious issues – all of which can have far-reaching and long-lasting consequences for both the patient and the healthcare organization. Routine patching helps keep the devices functioning and up-to-date, and should always be the first step taken to address any cyber risks.
Unfortunately, it’s not as simple of a fix as it may sound. Patching medical devices can often take time and extensive resources due to regulatory constraints and slow movement by manufacturers. However, despite these challenges, patching is a necessary part of a hospital’s IT strategy. Operating unpatched medical devices endangers your organization.
Risks of Unpatched Medical Devices
Manufacturers release new medical device patches after intensive testing. They may address security vulnerabilities but also include new features and improvements.
Ignoring these updates is incompatible with hospital goals. Unpatched medical devices have severe short and long-term consequences. Immediate problems that might arise include cyberattacks and device malfunctions due to the lack of updates. Over time, new issues spring from the original problems. Organizations may face hefty HIPAA fines, reputational damage, decreased business operations, or even more cyberattacks.
Cyberattacks lead to financial strain and a damaged reputation. Poorly functioning medical devices impact patient care and cause additional costs for repair or replacement. Cyberattacks are often financially draining. The average healthcare data breach costs $10 million.
In 2020, the Florida Healthy Kids Corporation learned that its web hosting provider had neglected to patch seven years’ worth of critical vulnerabilities. Cybercriminals exploited the lapse and breached sensitive networks.
According to the HHS’ Office for Civil Rights, 3.5 million patients were affected. Hackers gained access to full names, addresses, social security numbers, and more intimate data.
The financial impact of unpatched devices is significant, and hospitals must absorb the costs associated with any repairs, ransoms, HIPAA investigations, and client losses if they don’t take proper actions to protect themselves.
Strategies for Effective Medical Device Patching
Effective medical device patching requires rigorous strategies, including:
Developing a patch management plan
Consider taking a proactive approach to patch management. Schedule regular checks for new patches and commit to consistent implementation.
A strong patch management plan will outline clear responsibilities and timelines for your team.
Test patches before deployment
It’s essential to test patches before deploying them to the entire network. Testing reduces the risk of compatibility issues and prevents costly downtime or data loss.
Before applying the patch to your network, test it on a subset of devices or systems and look for any issues. Does the device still function? Is access still privileged? If you don’t find a problem, introduce the patch more broadly.
Stringent testing reduces risk. To protect your organization further, it’s necessary to have a plan for reversing patches as well. Potential issues may not arise until after deployment.
Coordinate with providers and manufacturers when possible
Patching requires coordination between multiple entities such as the device manufacturers, operating system provider, and internal teams. OS providers and manufacturers create, test, and distribute new patches. Health organizations implement the upgrades.
To make this process easier, develop direct communication channels with manufacturers. Your connection will help keep you informed of new patches for vulnerabilities you might not have identified yet.
Document the process
Documenting the patching process is a critical part of keeping medical devices secure.
Your documentation should include the time and date of the installation, who performed it, and any other changes made during the process. By doing this, you’ll be able to track down issues when they arise quickly and maintain full compliance in an industry full of stringent regulations.
Train staff
A big part of successful patching is having a properly trained staff. Provide your IT team with the necessary training to correctly understand and carry out the process. Your team should also know the risks associated with not patching and understand how to respond in an emergency.
To take your security a step further, include your entire healthcare staff in trainings on how to identify cyber risks within the network of devices they operate daily. Maintain efficiency by hosting training sessions regularly throughout the year. Cyber threats constantly shift, evolve, and grow in their sophistication.
Identifying and Prioritizing Unpatched Medical Devices
Identifying unpatched medical devices is the first step in successful patching. You need an up-to-date inventory of all your devices, including those used for clinical and nonclinical purposes.
Check your patch log and look for devices that haven’t been patched in 12 months or more. You can find new patches through the manufacturer’s website or the device’s software.
Once you have this information, prioritize devices based on the severity of their vulnerabilities and the criticality of their roles in patient care. Devices associated with high-risk processes should be at the top of your list.
Your patching efforts should also prioritize devices that are the most exposed to cyberattacks. These include those that connect to public networks or can provide access to sensitive data. Your relationships with manufacturers can help ensure timely patching when new security risks appear.
Patching is one of the simplest ways to protect against medical device vulnerabilities, but it’s far from your only option. Each manufacturer’s patch test and distribution timetable may be too slow to be reliable.
Additional security controls will further mitigate your hospital’s risk of cyberattack.
Why Patching Alone Isn’t Enough
Patching is an essential step in securing medical devices, but it isn’t enough on its own.
In the larger tech world, patching is a swift, agile process. But in the medical device industry, it can be a slow and arduous endeavor. Manufacturers must thoroughly test new patches before releasing them, often leading to lengthy approval processes.
Medical device patching is so time-consuming and complicated that, in fact, many devices will never have a validated patch available. Unique constraints make it impossible.
One factor is time. The massive number of potential vulnerabilities forces manufacturers to focus on the most critical patches. Time also affects the devices. Medical devices are aging fast in an industry that’s struggling to keep up with costs. There may be no patch available because the software is no longer supported.
Another factor is patient need. Most computers can be turned off without negative consequences. Medical devices are different. Patients may require continued, 24-7 device functioning, making it far more difficult to implement a patch.
Relying on patching alone leaves you exposed to numerous threats. In addition to patching, your hospital should take additional security measures, such as macro and targeted segmentation.
A Holistic Approach to IoMT Security
Vulnerability Management for IoMT devices requires a holistic approach. We’ve identified at least eight steps to mitigate IoMT cyber risk:
- Patching
- Macrosegmentation
- Targeted segmentation
- Configuration changes (Device Hardening)
- Micro-segmentation
- Upgrade or replace
- Accept the risk
- Building a holistic IoMT security program
Step #1: Patching
Patching is the most crucial step of any security program, and it’s the first line of defense for IoMT devices. However, patching can be a slow process with medical devices due to strict testing requirements.
Step #2: Macro-Segmentation
Macro-segmentation provides an extra layer of protection by splitting your network into broad segments, limiting the reach of an impacted device. Cyber attacks are far less effective when isolated to a single, small network.
Step #3 Targeted Segmentation
A more exact form of segmentation is to split devices by their likely exploit vector. This segmentation tactic requires software to analyze factors like device model, OS version, and connectivity.
Step #4 Configuration Changes (Device Hardening)
If you lack software for targeted segmentation, try device configuration changes. Simply check the device’s settings and apply the necessary changes. For example, you may need to disable a port. This strategy is time-consuming but effective.
Step #5 Micro-Segmentation
Micro-segmentation, also known as virtual segmentation, is a security technique that isolates critical systems on the same physical network or server. Distinct policies control who has access to each network zone.
Step #6 Upgrade or Replace
If patch management fails, a device may need to be upgraded or replaced. This option is only viable if everything else has proven unsuccessful. Replacing a clinically viable device is expensive and may not reduce your risk profile, as the new device will carry its own vulnerabilities.
Step #7: Accept the Risk
Sometimes, despite all of your efforts, there may still be irreconcilable vulnerabilities. In those cases, accept the risk, monitor the situation, and mitigate the damage if an attack occurs.
Step #8 Build a Holistic IoMT Security Program
A holistic security program takes into account all potential threats to your medical devices and implements measures to remove them.
Learn how to remediate cyber risk in your medical devices by downloading our step-by-step guide. And don’t miss out on the insights provided in the Cybersecurity IoMT Webinar Series where Sr Director of Solutions Engineering, Luke Smith dives into these 8 Steps further! Watch it on demand now.
Mitigate Medical Device Cyber Risk with Asimily
Let the experts take care of your device safety. Asimily is the leading IoMT risk remediation platform that provides hospitals and laboratories with reliable service. Our software helps you keep your devices safe.
With Asimily, you can maintain a comprehensive inventory with more than 100 data points about each device, including manufacturer, brand, serial number, port number, and more. This data makes cybersecurity patching more efficient and reliable.
Our platform continuously monitors for attacks and emerging vulnerabilities. Machine learning helps Asimily predict the baseline behavior for each device. Detailed forensics keep you aware of every possible anomaly.
Schedule a consultation with an Asimily expert to see how you can defend your healthcare systems against ransomware and malware attacks with our leading risk management platform for connected devices.
Secure Every IoT Device.
Automatically.
Cyber threats move fast — so should you. Asimily gives instant inventory and smart, prioritized risk mitigation insights for every IoT, OT, and IoMT device — so you can take action before threats strike.




