3 Key Security Lessons from Recent Healthcare Cyber Attacks

Healthcare has always been a target for threat actors. As an industry, healthcare organizations have a low tolerance for downtime and often limited funds to support securing critical data and medical technology from cyber threats. Nevertheless, healthcare as an industry needs to improve its defenses to ensure that patients can be taken care of in a safe and effective way over the long term.
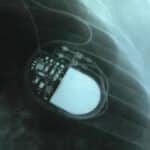
This is especially true as more medical equipment becomes accessible over the internet. Connected medical devices, also known as the Internet of Medical Things (IoMT), present new risks and new security challenges.
There are object lessons to be had in recent healthcare cyber attacks that offer insight into improving overall security posture. The attacks that will be examined here are the Ascension Healthcare compromise of May 2024, the Change Healthcare attack of February 2024, and a Russian cyberattack on hospitals in London from June 2024.
Ascension Healthcare: The Importance of Layered Defenses
Ascension Healthcare is the largest nonprofit Catholic health system in the country. It manages 2,600 healthcare facilities in 19 states, including 142 hospitals and 90 skilled nursing facilities. On May 8, the Ascension Healthcare IT team detected unusual activity on their systems. They confirmed the ransomware attack on May 9, and subsequent reports pointed to the Black Basta gang as the responsible group.
In the immediate aftermath of the attack, Ascension experienced substantial operational issues. Their electronic health record system was unavailable, and multiple hospital facilities had to divert patients to other locations because they could not provide adequate care to patients.
It took until June 14 to restore operations across the entire Ascension network that was affected. Patients in the states that Ascension serves could not access their patient portal until this time, and there remains the issue of uploading patient records taken between the incident on May 8 and the restoration of services on June 14.
The Black Basta attack originated with a spearphishing attack that gained them a foothold on a single device. Threat actors were able to lie in wait on the network for several weeks, harvesting credentials and elevating their privileges to eventually encrypt systems and exfiltrate personal health information.
One of the biggest lessons from the Ascension attack is to ensure there are layered defenses in place as well as anomalous behavior monitoring. Layered defenses that limited device permissions and communications throughout the network only to what is essential could have stopped this attack in its tracks. Adding anomalous behavior monitoring also would have theoretically alerted Ascension Healthcare IT to devices that had been compromised. That anomalous behavior often is a sign of threat actor activity, and looking for that could mean an early warning.
Change Healthcare: Supply Chain Attacks Need to be Addressed
The ransomware attack on Change Healthcare in late February 2024 that forced the company to disconnect over 100 systems has proven to be the largest healthcare breach in many years. The BlackCat/ALPHV ransomware gang claimed responsibility for the hack, which resulted in Change Healthcare customers being unable to process payments and collect revenue in their operations. Change managed more than 15 billion transactions in 2023 for a total of $1.5 trillion in revenue collected. This makes the company a significant player in the healthcare ecosystem.
Change Healthcare is a major supplier of payments processing for a huge swath of the American healthcare system. Roughly one third of all health insurance transactions flow through the Change Healthcare system, and the attack meant that those customers — from large hospital networks down to small physician-owned businesses — suddenly couldn’t get reimbursed or pay their employees.
The fallout from the attack meant that patients couldn’t receive care in many facilities nationwide, in addition to the exfiltration of patient data on what could be roughly one third of Americans. Change has said that they’ll begin notifying affected individuals in early July.
The Change Healthcare attack occurred because the company had not implemented multi-factor authentication on one of its critical services, according to a statement that UnitedHealth CEO Andrew Witty made to the U.S. House Energy and Commerce Committee when he was called to testify in May. That lack of MFA protection allowed the service to act erratically, and enabled BlackCat/ALPHV to escalate privileges to eventually encrypt services and extract data.
The key lesson here, beyond having a plan for a compromise of a critical supplier, is for healthcare organizations to implement basic security hygiene practices such as multi-factor authentication and the principle of least privilege for access. These basic tactics ensure that no single credentialed user has broad-enough access to cause major issues should their credentials be stolen.
Synnovis Attack: Ransomware and Delays in Care
Synnovis, a partnership between two London-area hospitals and SYNLAB to provide pathology services, was forced to destroy 20,000 blood samples because of a ransomware attack in early June. The attack also resulted in cancer-related surgeries getting canceled because the hospitals would not have been able to provide blood transfusions to any patients who needed one.
More than 1,130 planned operations and 2,190 outpatient appointments have been postponed at London hospitals—the King’s College Hospital NHS Foundation Trust and Guy’s and St Thomas’ NHS Foundation Trust experienced the biggest impact.
This sort of delay in care is part and parcel with ransomware attacks on healthcare providers. The Russian ransomware gang Qilin, responsible for the attack, said in a statement that they used a zero day to breach Synnovis. They also claimed a political motivation for the attack, which isn’t in keeping with their historical opportunism.
Healthcare Organizations Need Better Protection
Healthcare providers and hospital networks are under threat from threat actors all the time. Of the 1,193 ransomware attacks that the FBI tracked in 2023, the healthcare sector experienced 249 — or 20.9% — larger than any other critical infrastructure industry.
Protecting healthcare systems against ransomware can include deploying anomalous behavior detection, which is especially vital as more connected medical devices get deployed throughout healthcare provider campuses. It also means ensuring the use of strong access control for devices and users. Limiting privileges for employees as well as for connected equipment can ensure that threat actors have reduced opportunity to escalate privileges and compromise critical systems.
Anomalous behavior detection, like the kind that Asimily provides, drives better protection for healthcare systems. The ability to readily track how connected medical equipment is communicating with other devices on the network, and potentially communicating outside of the network, can help IT teams detect attacks in progress and lock them down far more efficiently.
Healthcare providers are going to continue to be a target for cyber criminals, whether they are financially or politically motivated. Ultimately, the best protection for these health systems is a good defensive strategy that integrates basic security hygiene practices, minimizing the impact of potential vulnerabilities, and implementing the right intelligence gathering for IT and security teams to make better decisions. Only then can healthcare providers confidently protect their critical systems and their patient data.
Secure Every IoT Device.
Automatically.
Cyber threats move fast — so should you. Asimily gives instant inventory and smart, prioritized risk mitigation insights for every IoT, OT, and IoMT device — so you can take action before threats strike.