Streamlined, Scalable Network Segmentation Orchestration
Labor-intensive segmentation enforcement becomes efficient, automated, and accurate with a continuous process.
Segment More Efficiently

Segmentation Simplified, Automated, Made Scalable
Transform segmentation efforts with contextual intelligence and actionable insights about every connected asset.
Get in TouchSmart Segmentation
Risk-Aware Insights Powering Dynamic Policies
Identify and Classify All Devices on the Network
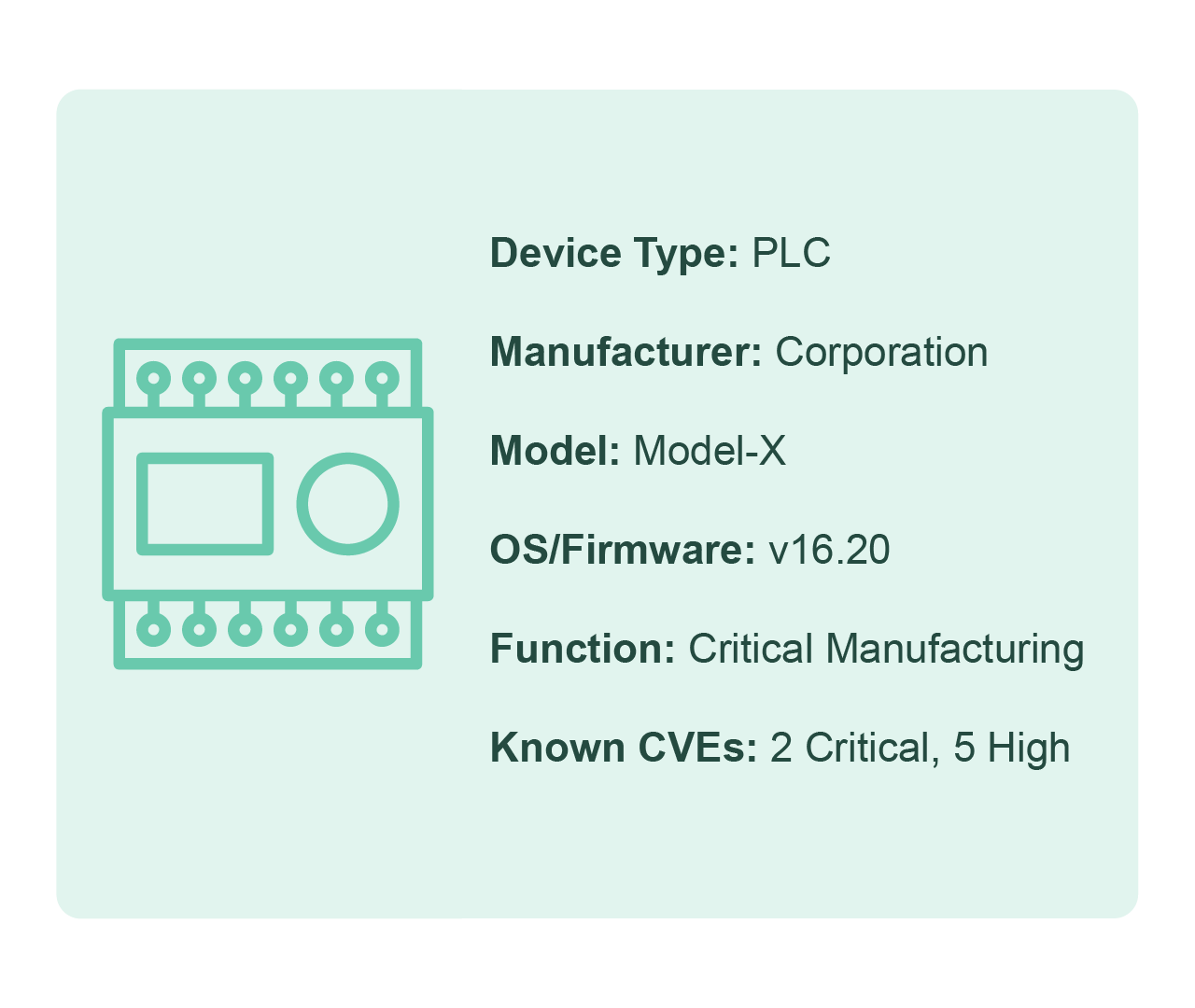
IP and MAC addresses aren’t enough. Asimily provides proper device context and real-time network insights to create segmentation policies that scale seamlessly with every IoMT, OT, IoT, and IT asset added to your network.
Map and Track Device Communication Patterns
Before you can segment safely, you need to understand how every device communicates – what it connects to, on which ports, using which protocols and services, and whether those connections are expected. Asimily maps these communication patterns in full detail to generate policies you can enforce with confidence that nothing breaks.
Prioritize the Most Critical Assets
Asimily’s risk-based prioritization takes the guesswork out of reducing the attack surface. By targeting the riskiest assets first, organizations can reduce exposure quickly and efficiently.

Create Safe and Enforceable Policies That Scale
The distinct operational nuances of medical, IoT, and OT devices must be carefully accounted for. Asimily determines what traffic to permit or restrict with a thorough understanding of what each device can and cannot support, and creates automated recommendations and segmentation groups accordingly.
Continuously Verify and Validate Policies
Segmentation is not a one-and-done process. Asimily continuously monitors policies to ensure effectiveness and can simulate segmentation scenarios to understand the impact of the policies being applied.
Secure Every IoT Device.
Automatically.
Cyber threats move fast — so should you. Asimily gives instant inventory and smart, prioritized risk mitigation insights for every IoT, OT, and IoMT device — so you can take action before threats strike.
Protecting Your Industry’s Unique Devices
Healthcare
Asimily provides the necessary tools to identify and address IoT vulnerabilities in healthcare, ensuring the protection of patient data without interrupting the delivery of critical care.
Discover MoreManufacturing
In an industry that relies heavily on IoT devices to drive automation, efficiency, and connectivity, Asimly can help. By ensuring the security of IoT devices, manufacturers can safeguard their intellectual property, prevent production disruptions, and maintain the trust of their customers and partners.
Discover MoreHigher Education
Educational institutions depend on interconnected devices to facilitate learning, research, and campus operations. Protect sensitive student and faculty data, maintain operational integrity, and foster a secure, productive academic environment with Asimily.
Discover MoreGovernment
Asimily equips government entities worldwide with the necessary tools to secure their IoT devices, protect critical infrastructure, and ensure data privacy. Defend against cyber threats and uphold public trust by proactively mitigating vulnerabilities.
Discover MoreLife Sciences
Where delicate research, development, and data exchange are ongoing, securing your IoT devices is a top priority. Proactively manage and mitigate vulnerabilities, reducing the risk of theft or loss of critical research and development efforts.
Discover MoreFrequently Asked Questions
Traditional network segmentation relies on IP addresses and VLANs, but IoT, OT, and IoMT devices have unique operational requirements that generic IT approaches can’t account for. Many connected devices use unexpected ports, proprietary protocols, or communicate with services that aren’t well-documented – so applying a blanket segmentation policy risks breaking critical workflows like patient monitoring or industrial control systems. Asimily solves this by deeply classifying every connected asset and mapping its full communication behavior – what it talks to, on which ports, using which protocols – so segmentation policies are built on actual device context, not guesswork.
Asimily continuously discovers and classifies every IoT, OT, IoMT, and IT device on your network, then maps each device’s real communication patterns in detail. From that intelligence, the platform automatically generates segmentation policy recommendations – specifying what traffic to permit or restrict – tailored to what each device can and cannot support operationally. This replaces the manual, spreadsheet-driven process most organizations struggle with and produces enforceable policies that scale as new devices join the network.
This is one of the biggest risks organizations face when attempting segmentation, especially in healthcare and manufacturing where device downtime can have serious consequences. Asimily addresses this by letting you simulate segmentation scenarios before enforcement, so you can see the impact a proposed policy will have on device communication and operations before anything changes in production. Combined with continuous monitoring after deployment, this ensures policies remain effective without disrupting critical services.
Network segmentation must be treated as a continuous process, not a one-time project. Devices are constantly being added, retired, updated, or reconfigured – and each change can invalidate existing policies. Asimily continuously monitors and validates segmentation policies post-deployment, flagging drift or gaps as your environment evolves. This ongoing verification ensures your segmentation posture stays aligned with your actual network, not a snapshot of what it looked like months ago.
Not all devices carry equal risk, and trying to segment an entire network at once is a recipe for stalled projects. Asimily uses risk-based prioritization to identify the most vulnerable and exploitable assets on your network, so your security team can focus segmentation efforts where they’ll reduce the most attack surface the fastest. By targeting the highest-risk devices first, organizations see measurable security improvement early – building momentum instead of getting buried in a years-long segmentation initiative.