Press Releases
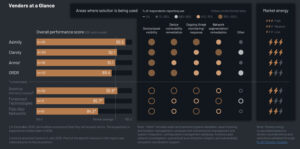
Media Mentions
Connect with Our Communications Team
If you’re a media representative or industry analyst and would like to engage with our team, please email us directly to info@asimily.com or leave a request via button below.
Contact Us